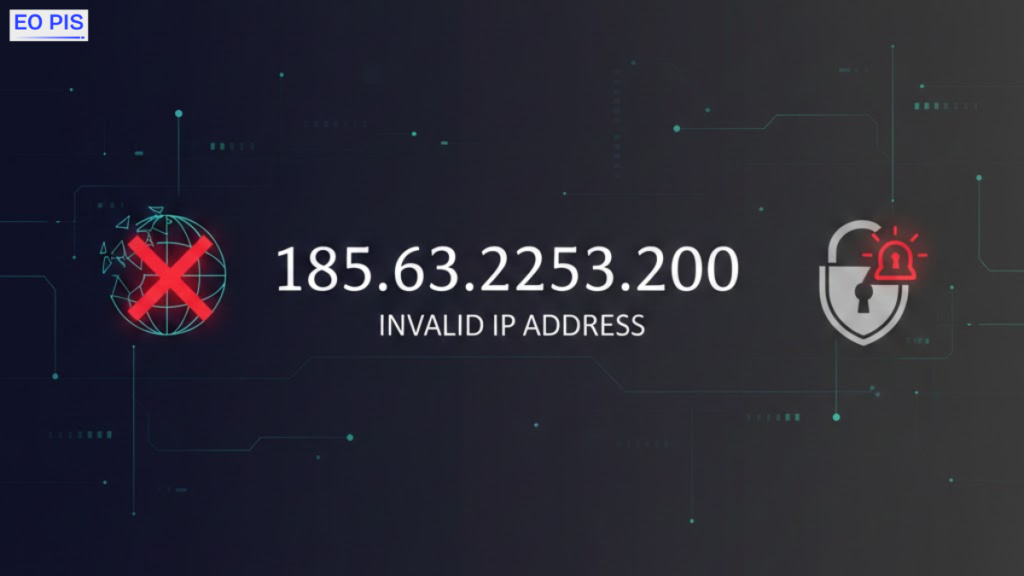
If you’ve encountered 185.63.2253.200, you’re likely trying to understand whether this IP address is legitimate, broken, or potentially dangerous. The reality is straightforward: the 185.63.2253.200 IP address is an invalid IPv4 address, but its appearance in logs, analytics, or systems can still signal technical or security concerns.
Knowing why 185.63.2253.200 is invalid, how IP address validation works, and when to investigate suspicious IP activity can prevent unnecessary panic while strengthening network awareness. For website owners, IT professionals, and even everyday users, recognizing malformed addresses helps avoid configuration mistakes and reduces IP security risks.
What is an IP Address and Why Does 185.63.2253.200 Matter?
An IP address is a core part of the Internet infrastructure. It acts as a unique identifier that allows devices to communicate using established network communication protocols. Without valid addressing, proper routing, and connectivity, it simply cannot happen.
When an invalid IP address appears, it matters because it can reveal misconfigured systems, input errors, or unusual activity. In real-world environments, unusual IP entries are often first noticed during log analysis, server troubleshooting, or security reviews. These moments matter because small anomalies sometimes expose deeper technical issues.
IP Address Fundamentals: The Basics You Need
To understand why this address fails, you need a basic grasp of the IP address structure. Most networks still rely on IPv4, which uses dot-decimal notation consisting of four number segments. Each segment must stay within the octet range 0–255 due to IPv4’s 32-bit addressing design.
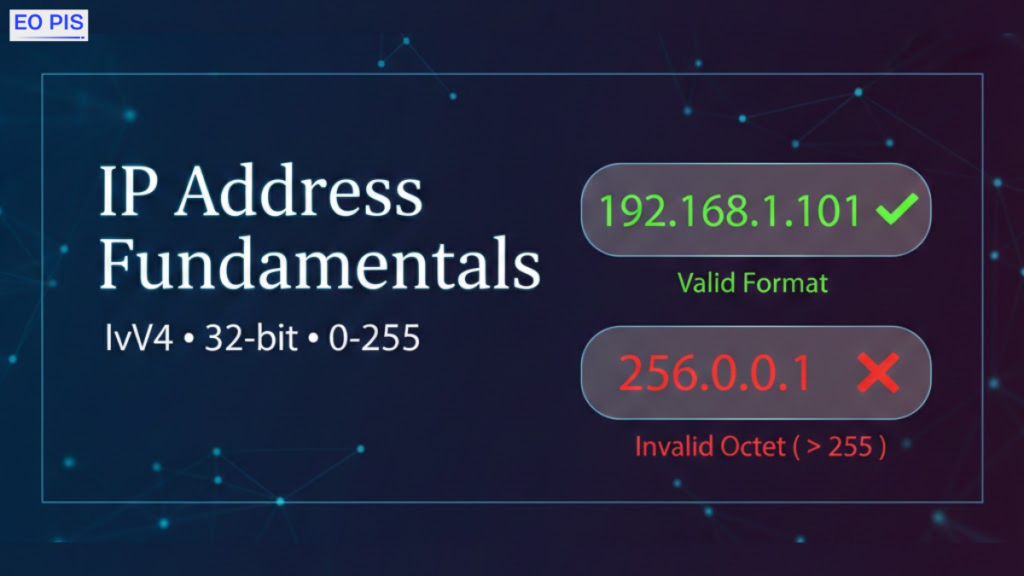
If even one number exceeds that range, the address becomes unusable. This rule exists because accurate formatting is essential for address resolution and stable network communication. Many connection failure causes in real systems come down to simple formatting mistakes.
What Is an IP Address & Types of IP Address
IP addresses serve different roles depending on how they’re assigned and used. Some are public and visible online, while others are private and limited to internal networks. They can also be static or dynamic, depending on whether they change over time through DHCP.
When errors occur, they often appear as a malformed IP address or as IP address errors in logs. A suspicious IP in logs doesn’t always mean a threat, but it always deserves context-based review. Many invalid entries originate from scripts, automation tools, or simple human input mistakes.
Internet Protocol Version 4 (IPv4) Explained Simply
IPv4 is still the most common version of the Internet Protocol. It relies on four numerical sections separated by periods. Each must follow strict limits to ensure proper communication across networks.
This structure exists to maintain reliable network communication protocols. When numbers exceed the allowed range, systems cannot process the address correctly. As a result, invalid entries typically fail immediately during IP address validation checks.
Internet Protocol Version 6 (IPv6) and How It Differs
Comparing IPv6 vs IPv4 highlights why formatting errors happen frequently. IPv6 uses a 128-bit IPv6 format with hexadecimal characters and a much larger address space. While it solves IPv4 exhaustion issues, most networks still operate primarily on IPv4, where formatting limits remain strict.
Invalid IPv4 entries often appear during system transitions, outdated configurations, or mixed network environments. This is especially common in enterprise systems that haven’t fully adopted modern addressing strategies.
Why 185.63.2253.200 Is Invalid
The address fails because one segment exceeds the permitted range. The number 2253 is higher than 255, which immediately breaks IPv4 formatting rules. This makes 185.63.2253.200 an invalid IPv4 address, and any system following standard validation rules will reject it.
Such errors typically originate from typing mistakes, broken scripts, or automated tools generating incorrect values. In some cases, developers use placeholder data during testing that accidentally appears in production logs.
Understanding the Structure of 185.63.2253.200 and Similar Addresses
Recognizing formatting issues improves network troubleshooting of IP processes. Any address that breaks IPv4 rules becomes unusable for routing. When repeated malformed entries appear in log analysis, they often indicate automation or configuration problems rather than real traffic.
A common misconception is that invalid addresses are harmless. In practice, frequent malformed entries can expose weaknesses in validation systems or monitoring setups.
Reasons Why 185.63.225.200 Is Showing in Google or Logs
Invalid addresses may appear online or in logs due to misconfigured tools, copied log data, or automated scanning scripts. Search engines sometimes index technical content that includes raw IP references, which is why these addresses occasionally surface in search results.
Within systems, such entries are usually discovered during network monitoring or routine IT troubleshooting. Their presence alone isn’t dangerous, but repeated appearances deserve attention.
Is 185.63.2253.200 Dangerous or Just a Typo?
Most of the time, it’s simply an error. However, context determines risk. If it appears once, it’s likely a typo or formatting mistake. If it appears repeatedly or alongside unusual traffic patterns, it could signal probing behavior or attempted IP spoofing.
From real-world observation, ignoring repeated malformed entries can delay detection of larger security issues. While invalid IPs rarely cause direct harm, they sometimes act as early indicators of deeper problems.
Potential Risks and Security Implications to Know
Invalid addresses can reveal configuration issues, automation errors, or suspicious probing attempts. In some scenarios, malformed traffic is used to test firewall protection or identify weak filtering rules. These patterns may also appear during attempted DDoS attacks or phishing campaigns.
Historical events like the Mirai botnet demonstrate how overlooked anomalies can escalate into significant disruptions. Monitoring and context-based analysis remain essential for strong server security.
You May Also Like 258.63.253.200: Is This a Valid IP Address?
Can Invalid IP Addresses Be Used in Attacks or Scams?
They can be used indirectly. Attackers sometimes send malformed traffic to observe how systems respond. Weak validation layers may allow unusual requests to pass through filters. This technique can reveal vulnerabilities before a real attack begins.
Security platforms and SIEM systems increasingly rely on AI-driven threat detection and machine learning to identify such anomalies quickly. Even so, human review remains critical.
How to Validate and Investigate This IP Address
Start by checking format rules and reviewing logs for patterns. Tools like WHOIS, ARIN, and RIPE help confirm whether similar addresses exist. Security platforms such as AbuseIPDB or VirusTotal provide additional context when investigating suspicious activity.
Advanced users often rely on Wireshark, Splunk, or ELK Stack for deeper analysis. Developers may automate checks using the Python ipaddress module to catch formatting errors early.
What Should You Do If You See This IP in Server Logs?
Stay calm and assess context. Verify that the address is invalid, review how often it appears, and check related system events. If patterns suggest automation or probing, apply appropriate filtering or monitoring.
Avoid a common mistake: reacting aggressively without understanding context. Many invalid entries result from harmless configuration issues rather than real threats.
Best Practices to Prevent IP Errors and Security Issues
Preventing issues starts with strong validation and monitoring. Systems should enforce strict formatting checks and maintain regular audits. Organizations benefit from aligning with frameworks like NIST 800-53 to strengthen compliance and cybersecurity best practices. Proper handling of IP-related data also supports GDPR and broader compliance and data protection requirements.
Advanced Insights: How Invalid IPs Affect Networks and SEO
Invalid IP entries affect more than connectivity. They can distort analytics, complicate monitoring, and create confusion during audits.
One overlooked reality is that malformed IP traffic can skew data reporting, leading to inaccurate performance insights. Another is that repeated invalid entries often come from automated scanning tools rather than direct attacks. Finally, poorly optimized validation processes can slow applications if systems repeatedly process incorrect input.
These insights highlight why proper validation and monitoring remain essential not only for security but also for performance and data accuracy.
Conclusion
The 185.63.2253.200 IP address is clearly an invalid IP address, but its presence still matters. It can reveal formatting mistakes, automation behavior, or early signs of cybersecurity risks. Understanding how IP validation works and responding with context-based investigation ensures stable systems and stronger security.
The practical takeaway is simple: validate first, review patterns carefully, and act only when necessary. In modern networking, awareness and proper validation are far more valuable than reacting to every anomaly.
FAQs
1. What is 185.63.2253.200, and why is it invalid?
185.63.2253.200 is an invalid IPv4 address because one of its sections exceeds the allowed range of 0–255. IPv4 formatting rules are strict, so any number outside that range makes the entire address unusable.
2. Is seeing an invalid IP address in logs a security threat?
Not always. A single invalid IP usually comes from a typo or system error, but repeated appearances may signal automated scans, misconfigured tools, or early probing attempts that deserve investigation.
3. How can I quickly check if an IP address is valid?
Check whether the address has four numeric sections and ensure each number stays between 0 and 255. You can also use validation tools or simple scripts to confirm formatting and identify errors instantly.
4. Why do invalid IP addresses sometimes appear in Google search or analytics?
Search engines and analytics tools can index raw log data, forum discussions, or misconfigured tracking scripts. This can cause malformed IPs to appear publicly even though they aren’t functional addresses.
5. Should I block invalid IP addresses in my firewall or ignore them?
If the invalid IP appears once, blocking usually isn’t necessary. If it shows up repeatedly or alongside suspicious traffic patterns, adding filtering rules and reviewing system logs is a safer long-term approach.